Automated Volatility Plugin Generation with Dalvik Inspector
Introduction
In this blog post we will be demonstrating a new feature to the Dalvik Inspector tool, which we are planning on releasing this summer at Black Hat USA. Specifically we have added functionality to the Dalvik Inspector GUI for automatic Volatility plugin creation. To accomplish this, we have developed a simple to use interface, which allows an investigator to select which class members he or she wishes to be included in the plugin output. The generated plugin can then be used in Volatility against future memory samples to provide automatic analysis.
Automatic Plugin Generation
To demonstrate the automatic Volatility plugin generation feature of Dalvik Inspector, we will create a plugin that gives us the url of the Command and Control server of the Chuli malware that we described in a previous post.
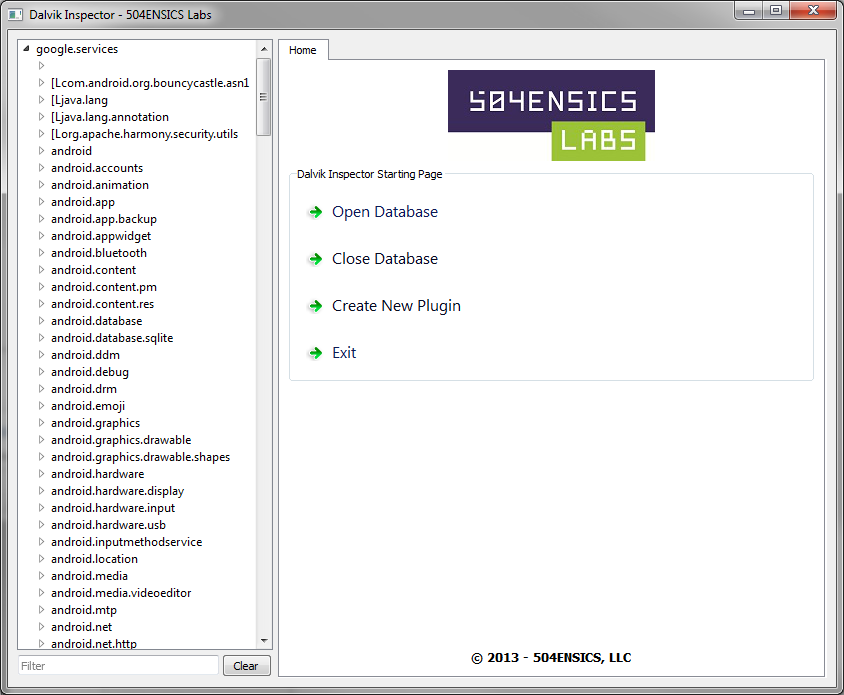
First, we open the database that was generated from our memory image by our Volatility plugin in Dalvik Inspector.
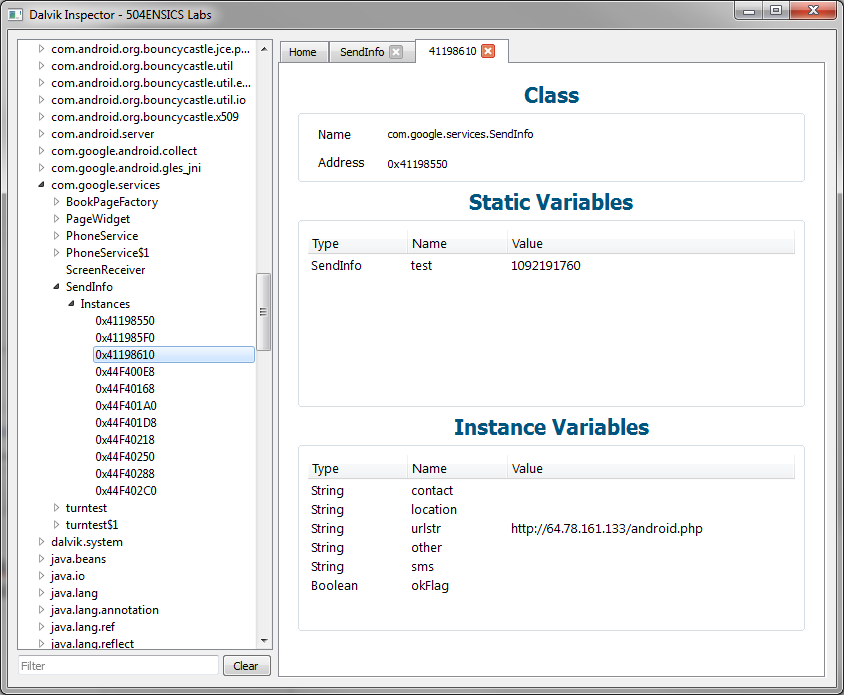
Using Dalvik Inspector, we can see that the command and control string is located in the urlstr field of the class, com.google.services.SendInfo.
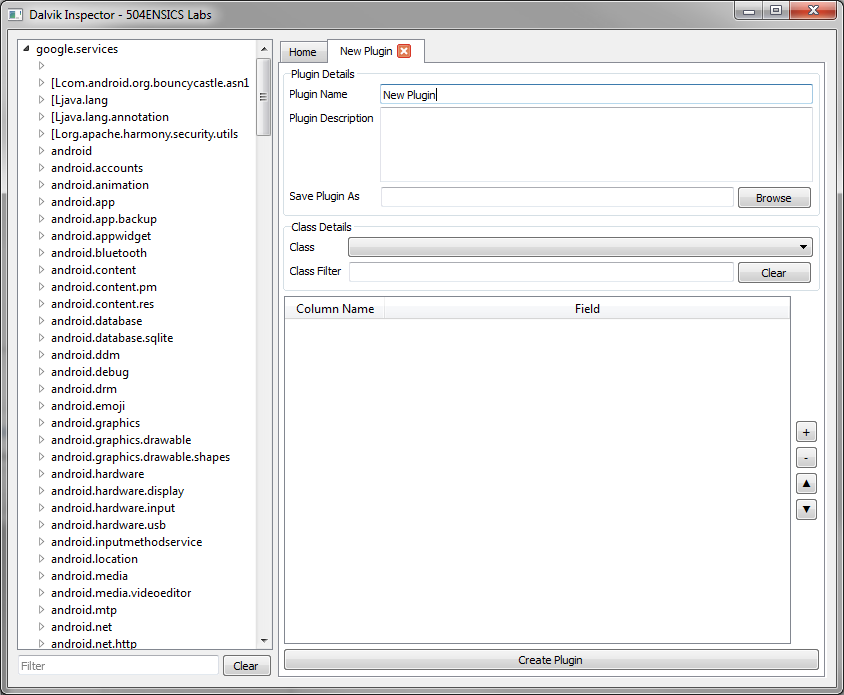
We navigate to the Home tab and select the new option, “Create New Plugin” and are presented with the following tab:
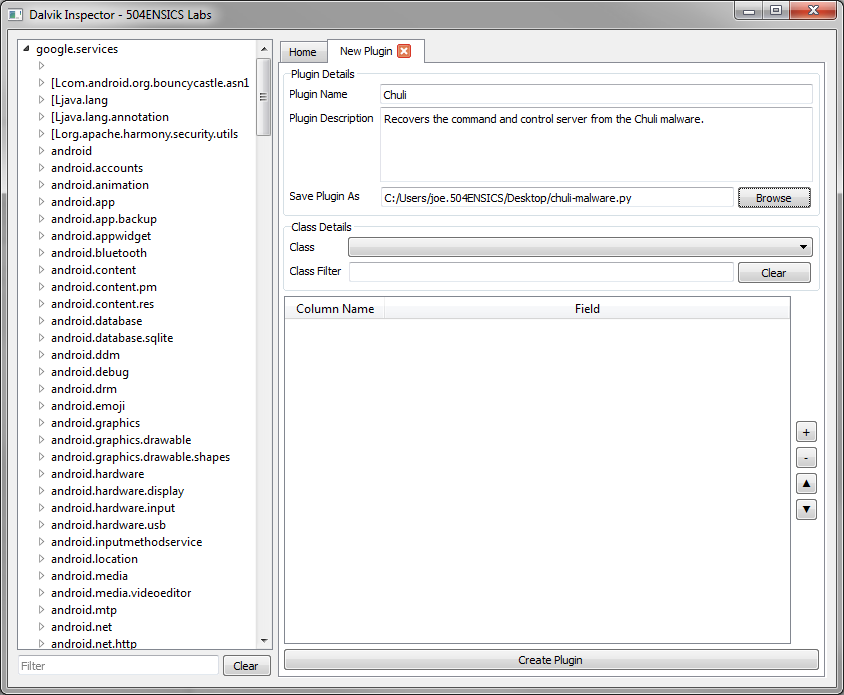
We first fill out the fields which give our plugin name, description, and the location where we wish the plugin to be saved.
We now must choose the class. Using the dropdown menu, we can see that there are a large amount of classes listed.
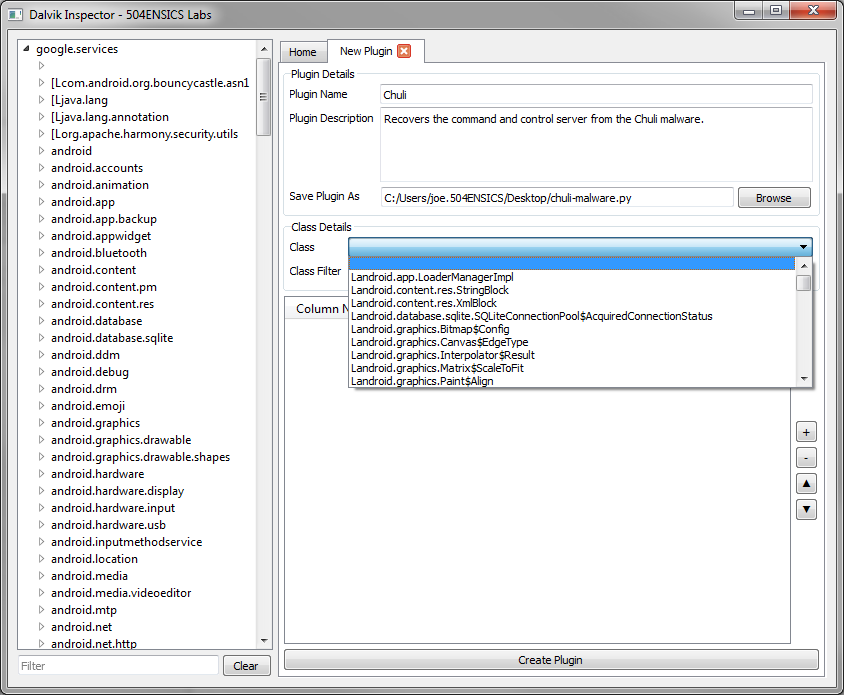
Because of this, the interface allows for filtering of classes. Since we know that we’re looking for the com.google.services.SendInfo class we simply type “services” in the Class Filter box.
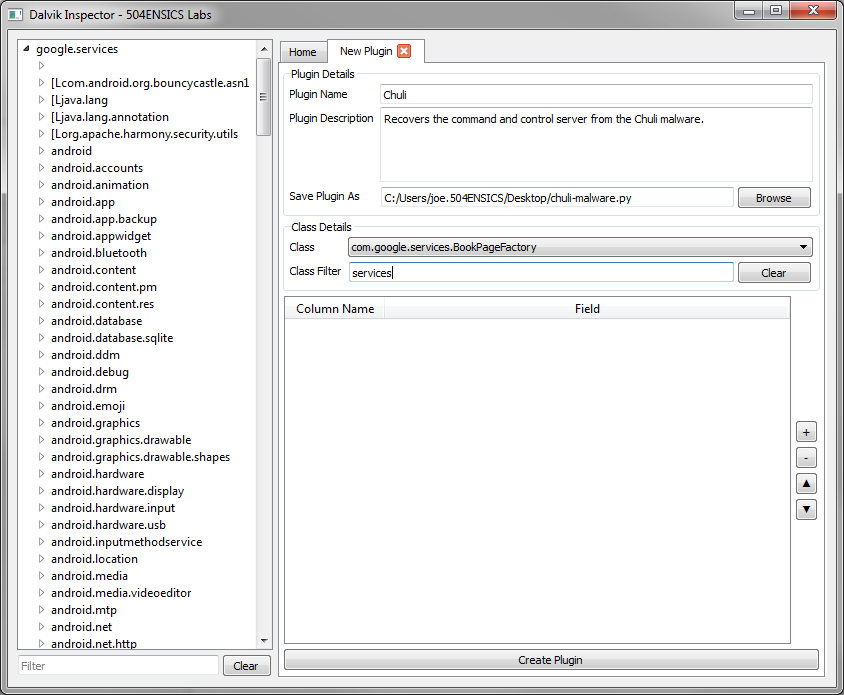
This filters the classes, only showing those which contain the word “services”. We can now easily choose our class.
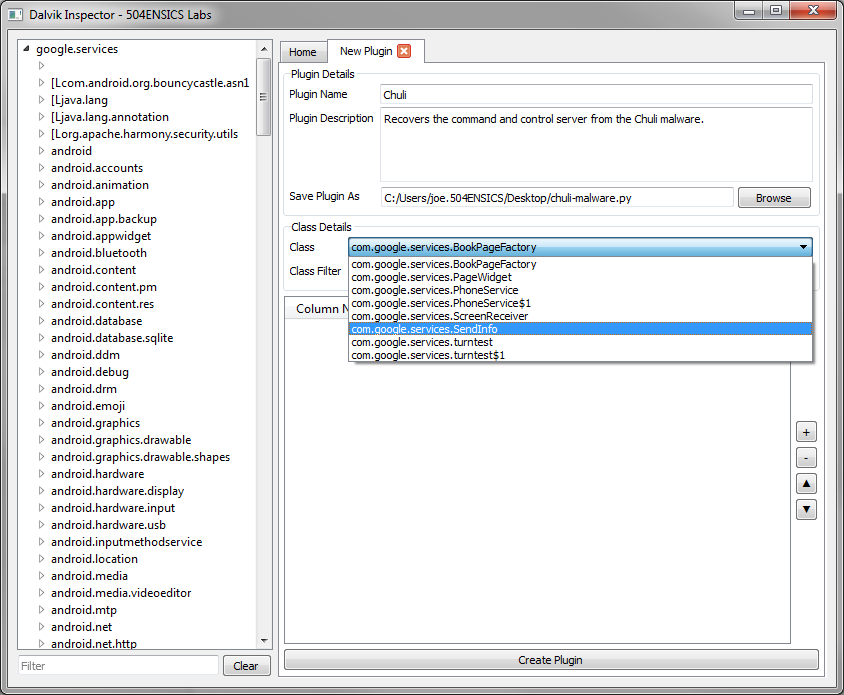
Next, we click the “+” button to add our field. We name the field “CCUrl” and choose the urlstr member.
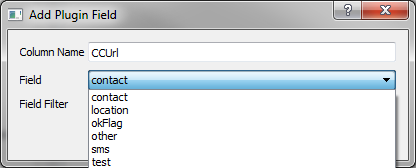
After clicking OK we can see that the field has been added. We could choose to add, remove, or change the order of the fields that we want to be displayed in the plugin, by using the buttons to the right. However, in this case we only care about the single field.
Clicking “Create Plugin” automatically generates our plugin and saves it at the path we selected.
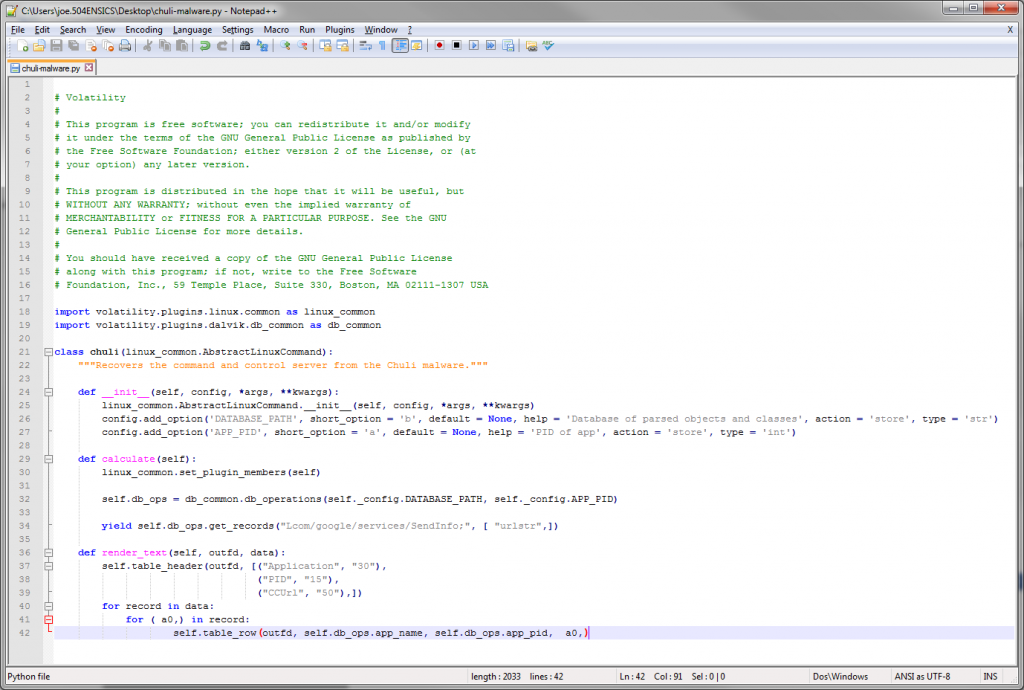
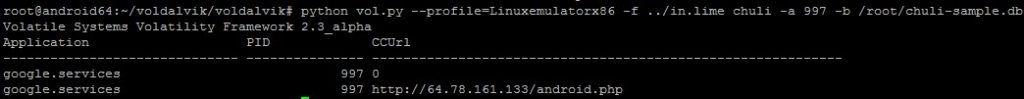
We add this plugin to Volatility and run it. For future memory dumps, this is the only step required.
Conclusion
We think that this feature of Dalvik Inspector will be very useful and will greatly simplify memory analysis of Android applications. Check back this summer for information about the Dalvik Inspector release!
About 504ENSICS Labs
504ENSICS Labs is a privately-owned firm, located in New Orleans, LA, offering a range of services including digital forensic investigation, network and application security audits, penetration testing, and training. To maintain our position at the forefront of the field, 504ENSICS Labs also specializes in cutting edge research and development of tools and techniques for digital forensics and computer security.
The co-founders, Lodovico Marziale, Ph.D. (CV) and Joe T. Sylve, M.S. (CV), are well known in the digital forensics and computer security research community, have published research in several peer-reviewed academic journals, and have presented their research at many conferences across the country.
